A comprehensive guide that demystifies the FedRAMP authorization process, breaking it down into clear, actionable steps from initial preparation through continuous monitoring.
Introduction: Navigating the Federal Cloud Landscape
Selling cloud services to the U.S. Federal Government offers a significant opportunity, but it has a major gatekeeper called the Federal Risk and Authorization Management Program, or FedRAMP. For many Cloud Service Providers (CSPs), the path to FedRAMP authorization appears complex and resource-intensive. This guide demystifies the process, breaking it down into a clear, step-by-step roadmap.
The Growing Demand for Secure Cloud Services in Government
Federal agencies are accelerating their migration to the cloud to modernize IT infrastructure, enhance efficiency, and improve citizen services. In fact, 45% of federal agencies now store citizen and mission data in the cloud, a number that continues to grow. This surge in adoption creates an urgent need for cloud solutions that meet the government's stringent security and compliance requirements.
What is FedRAMP?
FedRAMP is a government-wide program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. Established in 2011, its primary goal is to ensure the Federal Government has a consistent and effective risk management process for cloud adoption.
Why FedRAMP Authorization is a Game-Changer for CSPs
Achieving FedRAMP authorization is more than a compliance checkbox; it's a strategic business advantage. The "do once, use many times" framework is incredibly efficient—in FY22 alone, FedRAMP authorized products were reused more than 4,500 times across the government.
Understanding FedRAMP's Core Principles
FedRAMP's Roots: Built on NIST RMF and FISMA
FedRAMP is the implementation of the Federal Information Security Management Act (FISMA) for cloud services. The program's security framework is based on NIST Special Publication 800-53, which lists security and privacy controls for all federal information systems.
The Pillars of FedRAMP: Impact Levels
FedRAMP categorizes cloud services into three impact levels based on the potential impact of a security breach:
- Low: A breach would have a limited adverse effect on agency operations, assets, or individuals.
- Moderate: A breach could have a serious adverse effect. This level covers the majority of federal data.
- High: A breach could have a severe or catastrophic adverse effect.
Key Roles in the FedRAMP Ecosystem
- Cloud Service Provider (CSP): Your organization, responsible for implementing security controls.
- Federal Agency: The government customer that sponsors your CSO for authorization.
- Third-Party Assessment Organization (3PAO): An accredited organization that performs security assessment.
- Joint Authorization Board (JAB): Grants Provisional ATO (PATO) for CSOs with high reuse potential.
Strategic Preparation: Setting the Stage for Success
Self-Assessment and Readiness
Before engaging a 3PAO, conduct a thorough internal readiness assessment. This involves a gap analysis comparing your current security posture against required FedRAMP security controls. The cost of a formal Gap Assessment from a 3PAO can range from $30,000 to over $150,000.
Choosing Your Path: Agency Authorization vs. JAB PATO
There are two primary paths to FedRAMP authorization:
- Agency Authorization: The most common path. A specific federal agency sponsors your cloud service and issues an Authority to Operate (ATO).
- JAB PATO: A more competitive path where the JAB grants a Provisional ATO for high-demand services with broad government applicability.
Developing Your System Security Plan (SSP)
The System Security Plan (SSP) is the cornerstone of your FedRAMP documentation. This comprehensive document details every aspect of your system architecture, data flows, and how you have implemented each required security control.
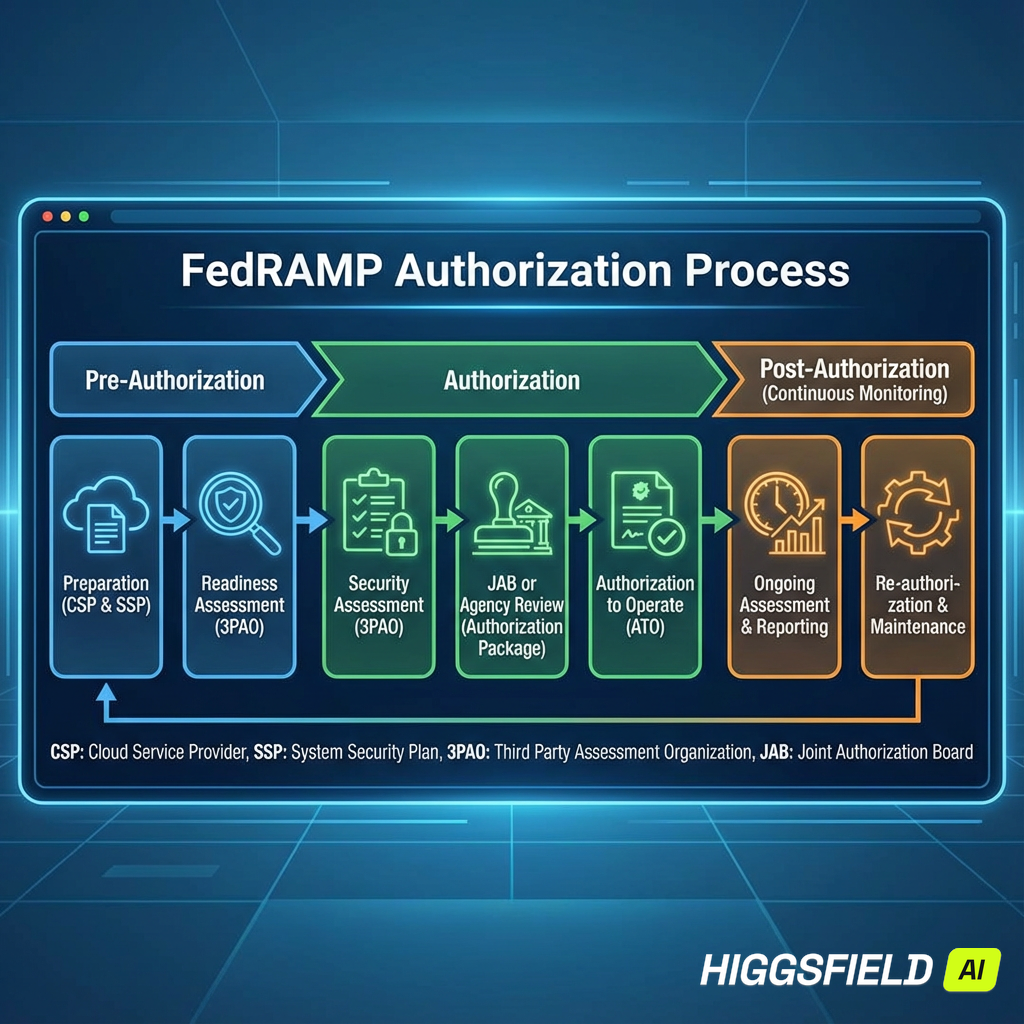
The Step-by-Step Authorization Journey
Step 1: Securing Agency Sponsorship
For the agency path, secure a partnership with a federal agency that wishes to use your cloud service. This agency becomes your sponsor and will ultimately issue the final ATO.
Step 2: Engaging a 3PAO
Select the right Third-Party Assessment Organization. They will independently validate that your security controls are implemented correctly and operating as intended.
Step 3: Conducting the Security Assessment
The 3PAO will perform a comprehensive security assessment, including vulnerability scanning, penetration testing, and document review. Findings are compiled into a Security Assessment Report (SAR).
Step 4: Remediation and POA&M Development
Create a Plan of Action & Milestones (POA&M) document detailing each finding, your proposed remediation plan, and timeline for completion.
Step 5: Achieving Your ATO
Submit the complete security package—SSP, SAR, and POA&M—to your agency sponsor. The Authorizing Official will review and, if acceptable, issue an Authority to Operate (ATO) letter.
Step 6: Listing on the FedRAMP Marketplace
Once you achieve an ATO, your cloud service will be listed on the official FedRAMP Marketplace, providing significant visibility to federal agencies.
Sustaining Compliance: Continuous Monitoring
The Core Principle of Continuous Monitoring
FedRAMP requires robust continuous monitoring (ConMon) to ensure your security posture remains strong. You must provide monthly ConMon reports to your sponsoring agency.
Managing Your POA&M Lifecycle
Your POA&M is a living document. As new vulnerabilities are discovered, they must be added with clear remediation plans. Proactive management demonstrates a mature security program.
Adapting to Evolving Standards
Stay informed of FedRAMP requirement updates, such as the recent shift to NIST SP 800-53 Revision 5, and adapt your security controls accordingly.
Beyond Authorization: Strategic Advantages
Unlocking Federal Contracting Opportunities
A FedRAMP ATO is the master key to the federal cloud market. It drastically shortens sales cycles as agencies can reuse your authorization rather than starting new security assessments.
Understanding FedRAMP 20x
The government is working to make FedRAMP faster through initiatives like FedRAMP 20x. Recent efforts have reduced some FedRAMP authorizations to approximately five weeks.
Conclusion
Navigating FedRAMP is demanding but achievable. It requires strategic planning, dedicated resources, and unwavering commitment to security. By understanding core principles, preparing documentation carefully, and following the step-by-step process, you can achieve an Authority to Operate and position your cloud service as a trusted choice for the Federal Government.